Linux Basics, Shell Scripting (2021-03-29)#
Agenda#
Day 1
Linux and UNIX concepts
Commandline: using the shell efficiently
Filesystem and permissions
Day 2
Tools:
cat,cut,head,tail,grep, and the likeThe pipe
Exercises: combine things to solve problems
Day 3
Shell scripting: Variables
Control flow:
if,whileExercises
Day 4
Functions
Subshells
Parameter expansion, here-documents, and more details
Exercises
Course Preparation#
We will be using a Linux machine somewhere in the cloud, IP address
34.107.39.200. Please verify that you are able to login as
follows (substitute my username with yours),
From a Linux system, use the
sshprogram (substitute my username with yours)$ ssh faschingbauer.joerg@34.107.39.200 The authenticity of host '34.107.39.200 (34.107.39.200)' can't be established. ECDSA key fingerprint is SHA256:/in22o4VCD400X0bb4FlCb5/vQnrvKvOirgfqq6maPo. Are you sure you want to continue connecting (yes/no/[fingerprint])? yes Warning: Permanently added '34.107.39.200' (ECDSA) to the list of known hosts. faschingbauer.joerg@34.107.39.200's password: Linux fh-ece-19 4.19.0-14-cloud-amd64 #1 SMP Debian 4.19.171-2 (2021-01-30) x86_64 The programs included with the Debian GNU/Linux system are free software; the exact distribution terms for each program are described in the individual files in /usr/share/doc/*/copyright. Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent permitted by applicable law. Last login: Sat Feb 27 15:04:09 2021 from 77.119.129.226 faschingbauer.joerg@fh-ece-19:~$
From a Windows system, use PuTTY to do the same.
Log#
Day 1#
Linux Basics (download), heading straight
through to the “Permissions” chapter startung on slide #92.
Exercises#
Change Password
Your password on our cloud machine equals your username. From a security standpoint, this is suboptimal - if anybody knows your username, you’re pwned.
Change your password.
Create an alias
ls -al DIRshows a long listing ofDIR(including “hidden” files).ls -alis relatively clumsy to type, clumsier than e.g.x.For your comfort, create an alias to solve this problem. Do this in a way that makes the alias automatically available on next login.
echosuppressing linefeedThe
echocommand appends a linefeed (aka newline) to its output,$ echo this is a line because it has a newline at the end this is a line because it has a newline at the end $
(You can see the newline character because the next prompt appears on a new line.)
Which option makes
echosuppress the newline character? (The next prompt appears right after the output, on the same line.)Show file content
In my (username
faschingbauer.jörg) home directory, there exists a subdirectorydumpbin, and inside that directory exists a fileeaster.Print the file content on the console.
Create dumpbin, and give colleagues write permissions
In your hmoe directory, create a
dumpbindirectory. Give your colleagues write permissions in that directory (btw, a colleague is one of thefrcollgroup).Create a file in your colleague’s dumpbin, and write-protect that file against the colleague
Day 2#
Again from Linux Basics (download)
Permissions, again (this is important!)
Tools, including some live demos of pipe usage
stdin,stdout, pipe short demos
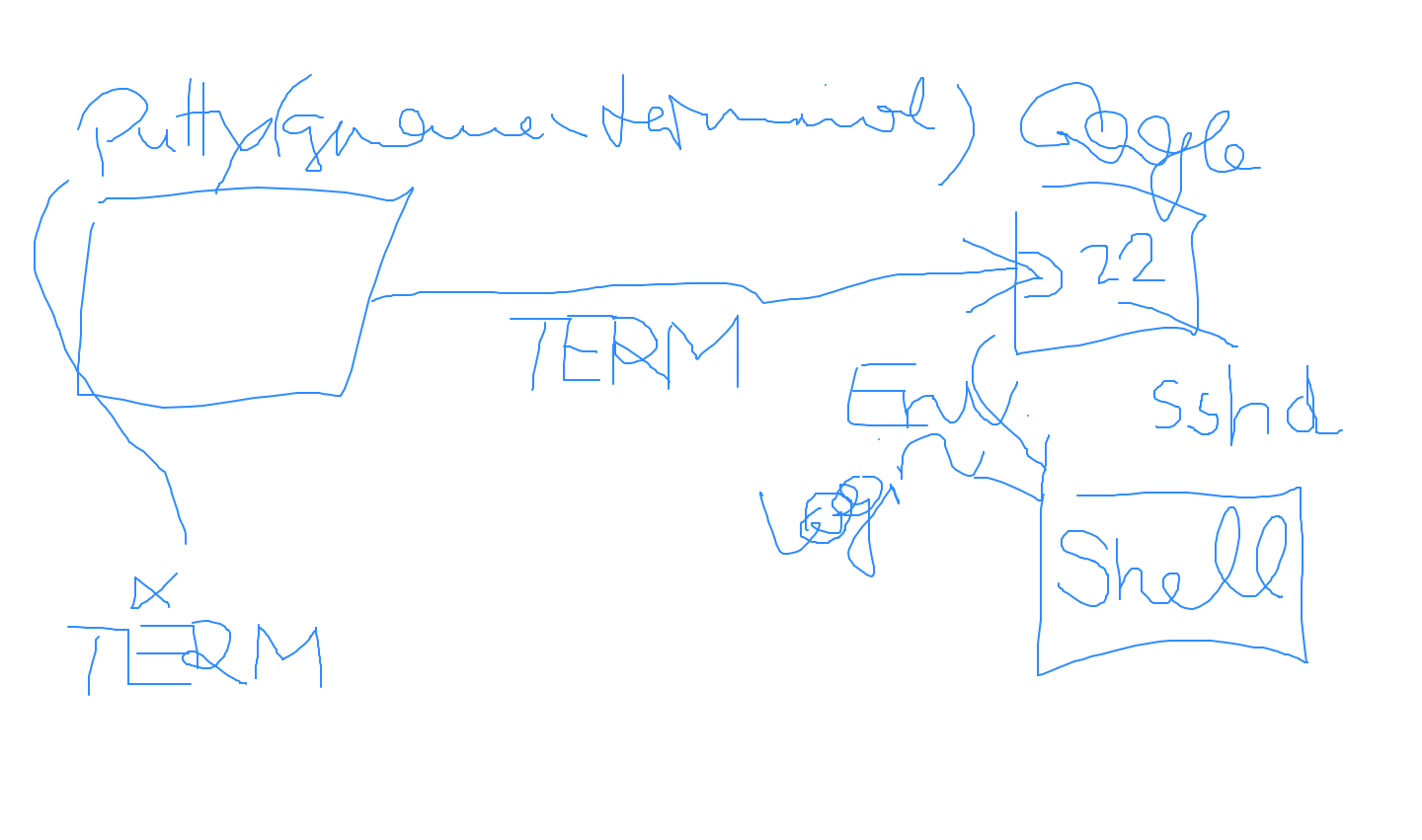
How PuTTY/SSH terminals play together with the SSH daemon (the
$TERM environment variable)#
Day 3#
More about SSH (
download slides)From Linux Basics (
download)IO Redirection and Pipes
A bunch of exercises from that same chapter
Day 4#
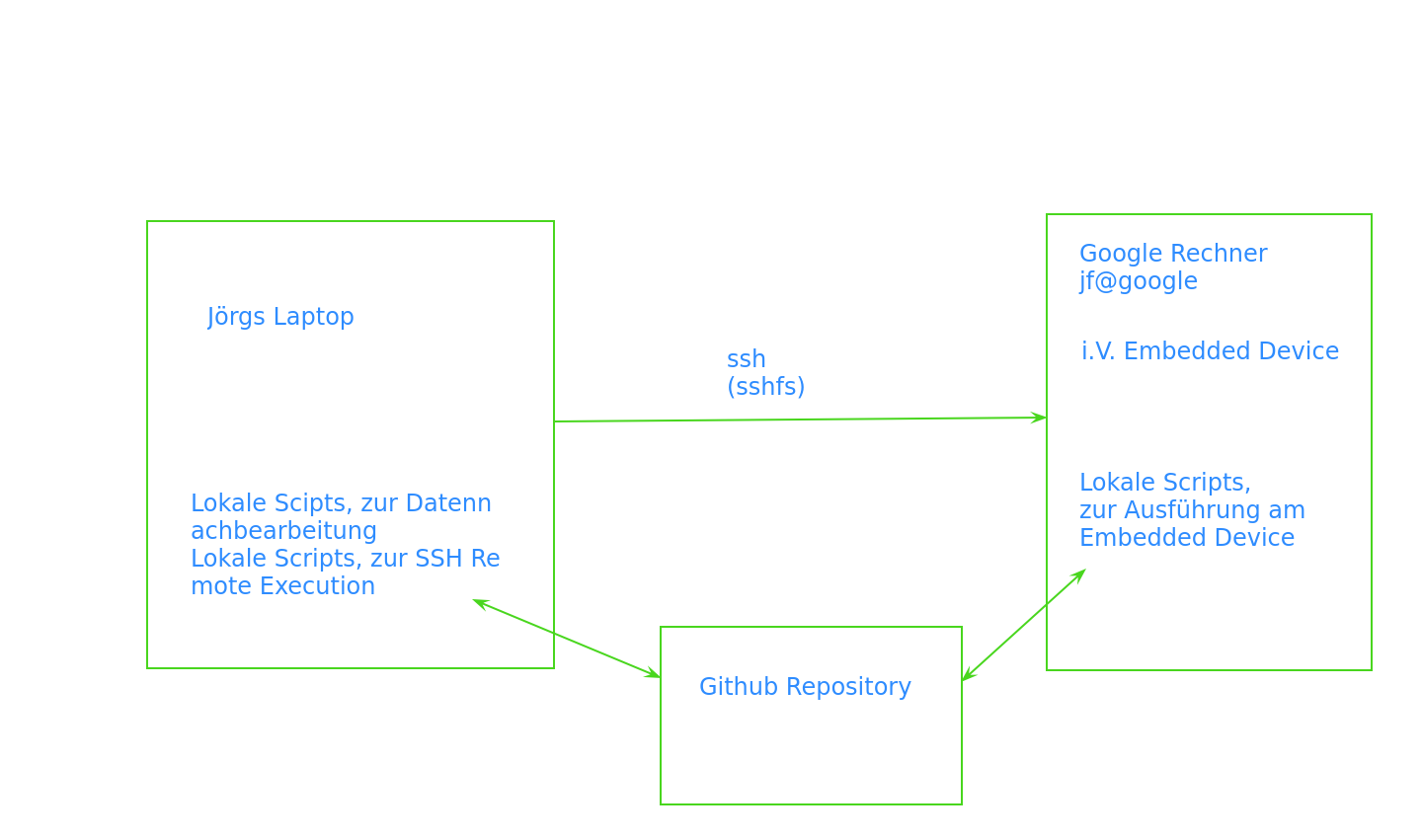
Problem: on the (small ARM) target machine hell breaks loose (OOM killer runs amoc) from time to time. Sketch a possible way to pull memory usage snapshots from the target.
SSH for remote execution
Shell script on target
Python on host, after making clear why Shell is not an appropriate language if you want to do more.
Links#
SSH#
Beginners
Tinkernut has a lot about Raspbery, here’s something he has about SSH.
Key base authentication, including turning off password authentication on the server (definitely recommended if you intend to go public)
Corey Schaefer is into Python; he has a lot of awesome tutorials, from beginner stuff to very advanced.
SSH tunneling. We didn’t get to that. Again from Tinkernut.
Linux and/or Shell on Windows Host#
On day 4 we sketched how host/target integration could work: running programs/scripts on the host, and automating remote execution on the target (using SSH and key based authentication). Here’s a number of ways how to have a Linux (-like) environment on the (Windows) host.
Install any distribution on your PC (unlikely in a Windows centric company)
Run any distribution on VirtualBox
Cygwin is a rather lightweight alternative to all of above. All you need is a shell prompt, after all.
Git for Windows comes with a Bash and assorted tools.
Editor Support for Shell Scripting#
I definitely don’t recommend Emacs. But anyway, nano is not an editor which is made for programmers.
Visual Studio Code appears to be the Emacs for Kids Today. It comes with a large universe of programming language support,