Linux on Raspberry Pi#
Preparation#
Cloud Machine#
A machine has been setup somewhere in The Cloud, as a way of working together on one machine while we are physically far away from each other.
The machine’s OS is Debian 10.6 for that matter, which is similar to what we’ll encounter on the Raspberry - at least for the generic Linux part of the training.
ssh training@35.246.179.112
... leave passphrase empty ...
.. supply password sent in private email ...
Please try out your {login,connectivity,corporate firewall}, and
send feedback accordingly.
Raspberry on Participant’s Desks#
Please take care to have access to a Raspberry Pi.
This training is about using Raspberries to accomplish something. You might want to try things out on the Raspberry while doing the training exercises in the cloud.
Agenda#
This is a preliminary list of topics that we will cover. Please send suggestions to training@faschingbauer.co.at.
Overview of concepts
Commandline - the Bourne Shell
Filesystem
File Types
Tools (
cp,mv,rm, …)Permissions
More Commandine
More Tools:
grep,find,head,tailIO Redirection
The Pipe
Archiving and Comressing (
gzip/bzip2,tar)
Diagnosing
Processes:
ps,top, andprocfs(and scheduling in general)Network:
netstatandnetcat/nc
Shell Scripting
Syntax and Concepts
Control Flow:
if,while,caseFunctions, Blocks, and Subshells (optional, if there is time and interest)
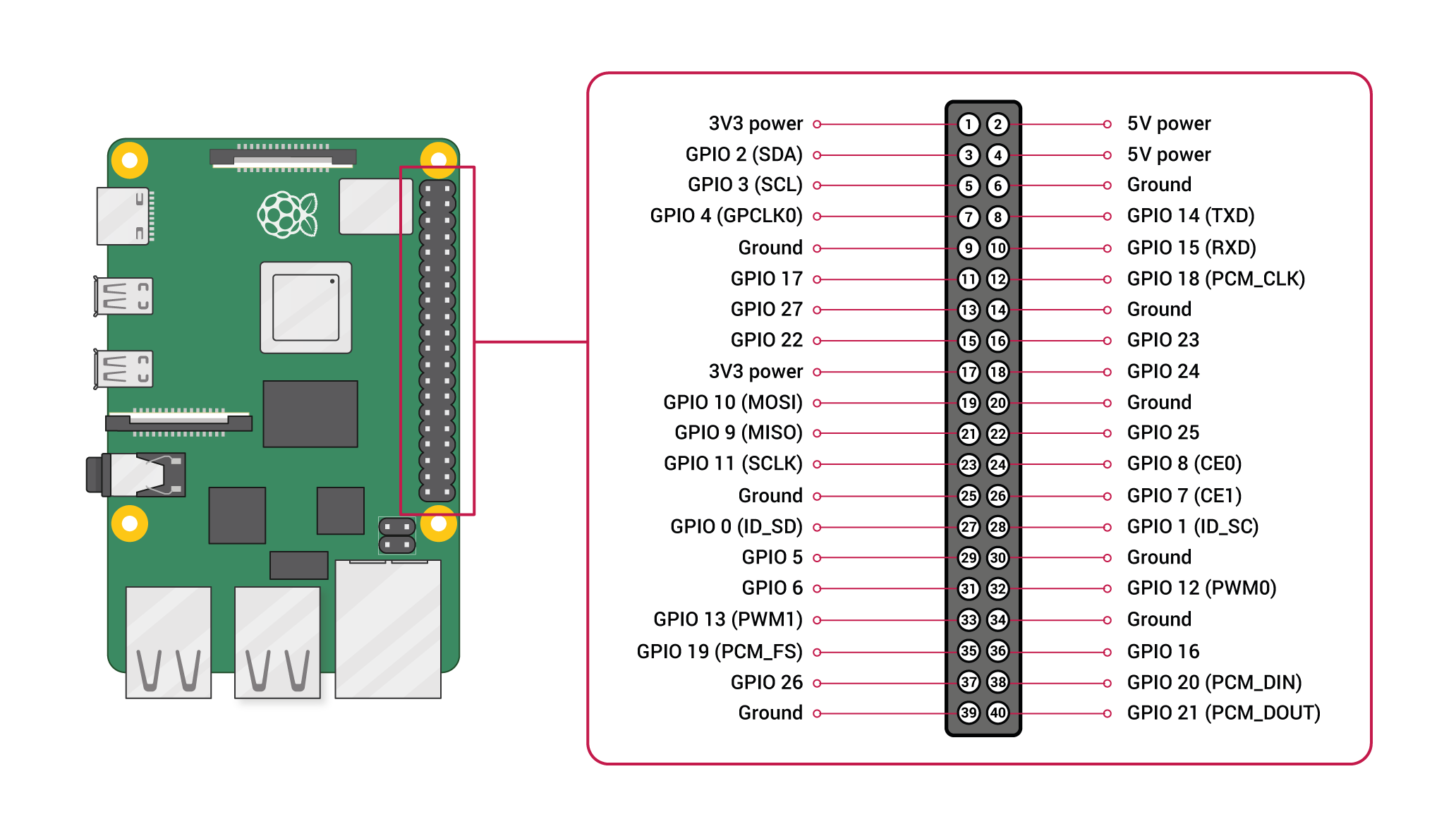
Raspberry Pi
GPIO subsystem
I2C: adding sensors (optional, if there is time and interest)
Serial/RS232 interface (optional, if there is time and interest)
Log#
Day 1#
(From the PDF slides)
Building blocks (complete)
Demo sessions (complete)
Bash (complete)
Filesystem
Paths
Directories
Symbolic links
Current working directory
Directory listings
Copying and moving
Day 2#
Filesystem
Owner, permissions
find
Tools for text files
Day 3#
Day 3 will happen on 2020-11-17. Following topics are on the menu:
Basic security#
Show
telnetdrunning. Blah old insecure blah.$ netstat -tn Active Internet connections (w/o servers) Proto Recv-Q Send-Q Local Address Foreign Address State tcp 0 0 192.168.3.70:22 192.168.3.1:34490 ESTABLISHED tcp 0 124 192.168.3.70:23 192.168.3.1:56062 ESTABLISHED
Service configuration:
sshd$ systemctl enable sshd ==== AUTHENTICATING FOR org.freedesktop.systemd1.manage-unit-files === Authentication is required to manage system service or unit files. Authenticating as: root Password:
Hm, don’t have a root password
Quickly recap setuid, using
passwdandsudosudo -i, to become rootSet root password
Back to unprivileged
pi$ systemctl enable ssh
(Supply root password)
Next:
systemctl start sshdLogin over ssh
Generate and deploy keys (for better security and interactive use)
Windows/Putty: https://www.ssh.com/ssh/putty/windows/puttygen
Backup
~/.ssh/; create empty oneGenerate keys
Deploy
id_rsa.pub: scp there, and append to (non-existing).ssh/authorized_keys. Trivia time: how append content to file?$ cat id_rsa.pub >> .ssh/authorized_keys
Demonstrate interactivity
Create a non
piuser with more restricted rights. Nothing, as a start. Enter GPIO.
Interlude: SD Card Setup (No Bloody Disk Imager)#
Hooray: Everything is a file
Raspberry SD card setup, not using any of these idiotic “Disk Imager” programs (hey, they even recommend using one on Ubuntu!)
GPIO, using sysfs interface#
Demo: scripting an LED blinker
In the Wild: Watchdog#
Use a watchdog program to check a script’s output. Verify that a file is modified periodically, for example. Write that script, based upon what we have learned in this training.
Miscellaneous#
Reload a page in Chromium. Hm, not sure if this is Linux Basics.
TODO#
Document network setup (
Documentation/Training-Network.rst); draw nice sketch